70% of companies have suffered a data breach in the last three years, and 77% of those breaches started with a third party, which is exactly why TPRM supplier assessment under DORA is now a board-level issue rather than a back-office chore.
Key Takeaways
| Question | Answer |
|---|---|
| What is a DORA-aligned TPRM supplier assessment? | It is a structured third party and supplier risk management process that maps vendor due diligence, contracting, and monitoring to DORA’s ICT and operational resilience requirements, often supported by AI tools such as the modular solutions on the Checkfirst solution page. |
| Why does DORA matter for TPRM in 2026? | DORA has been fully in force for procurement and ICT suppliers since January 2025, which means financial entities must evidence structured supplier assessment, testing, and continuous monitoring across all critical third parties. |
| How many vendors does a typical TPRM team cover now? | Companies work with an average of 286 vendors, so manual supplier assessments no longer scale without automation and strong data reuse across the TPRM lifecycle. |
| Where does AI help the most in TPRM supplier assessment? | AI supports document review, evidence extraction, questionnaire scoring, and scheduling of audits, similar to how ScheduleAI automates audit allocation and rescheduling for complex certification workflows. |
| What frameworks are commonly used for supplier risk assessment? | Security and ICT suppliers are increasingly assessed against CSA CCM, SOC 2, ISO 27001 and other frameworks that can be aggregated in AI-powered TPRM platforms like those described on CheckFirst. |
| How can teams keep a handle on operational chaos? | Centralizing supplier data, automating questionnaires, and connecting scheduling, inspection, and reporting modules, as in the digital inspection platform described in the Checkfirst digital inspection launch, gives risk owners visibility and control. |
1. What DORA Really Expects From Your TPRM Supplier Assessments
DORA is clear on one point: outsourcing never means outsourcing accountability, which means our TPRM supplier assessment process has to scrutinize every critical ICT and operational supplier as if their controls were our own. In 2026, supervisors expect not only written policies but evidence that we actually follow a risk based assessment lifecycle for each high impact third party.
For financial entities and TIC players serving them, this translates into structured supplier risk management across initial due diligence, contract clauses, testing, ongoing monitoring, and exit planning. DORA also explicitly calls for threat led penetration testing every three years for critical functions, annual ICT asset management, and continuous monitoring of high risk vendors, all of which feed directly into how we design TPRM workflows.
2. Why Traditional Supplier Risk Management Breaks Under DORA
Many TPRM programs still rely on spreadsheets, email threads, and static questionnaires, which quickly fall apart when you have hundreds of vendors, dozens of assessments in flight, and auditors asking for evidence for a specific quarter. The average TPRM professional now juggles dozens of suppliers at once, and every new DORA control, every new ICT incident, adds more noise to an already overloaded system.
The result is manual chaos, duplicated work, and high risk blind spots, especially around sub processors, concentration risk, and business continuity dependencies. With DORA in force, this is no longer just operational pain, it is regulatory exposure when a missing supplier assessment trail shows up during an on site inspection.
3. The Core Components Of A DORA-Aligned TPRM Supplier Assessment Framework
To reduce this chaos, we need a clear TPRM framework that connects supplier assessment activities to DORA articles and to the underlying ICT and operational risks. At a minimum, a DORA aligned framework for supplier risk management covers classification, due diligence, contracting, technical and operational testing, and continuous monitoring, all tied to a documented risk appetite.
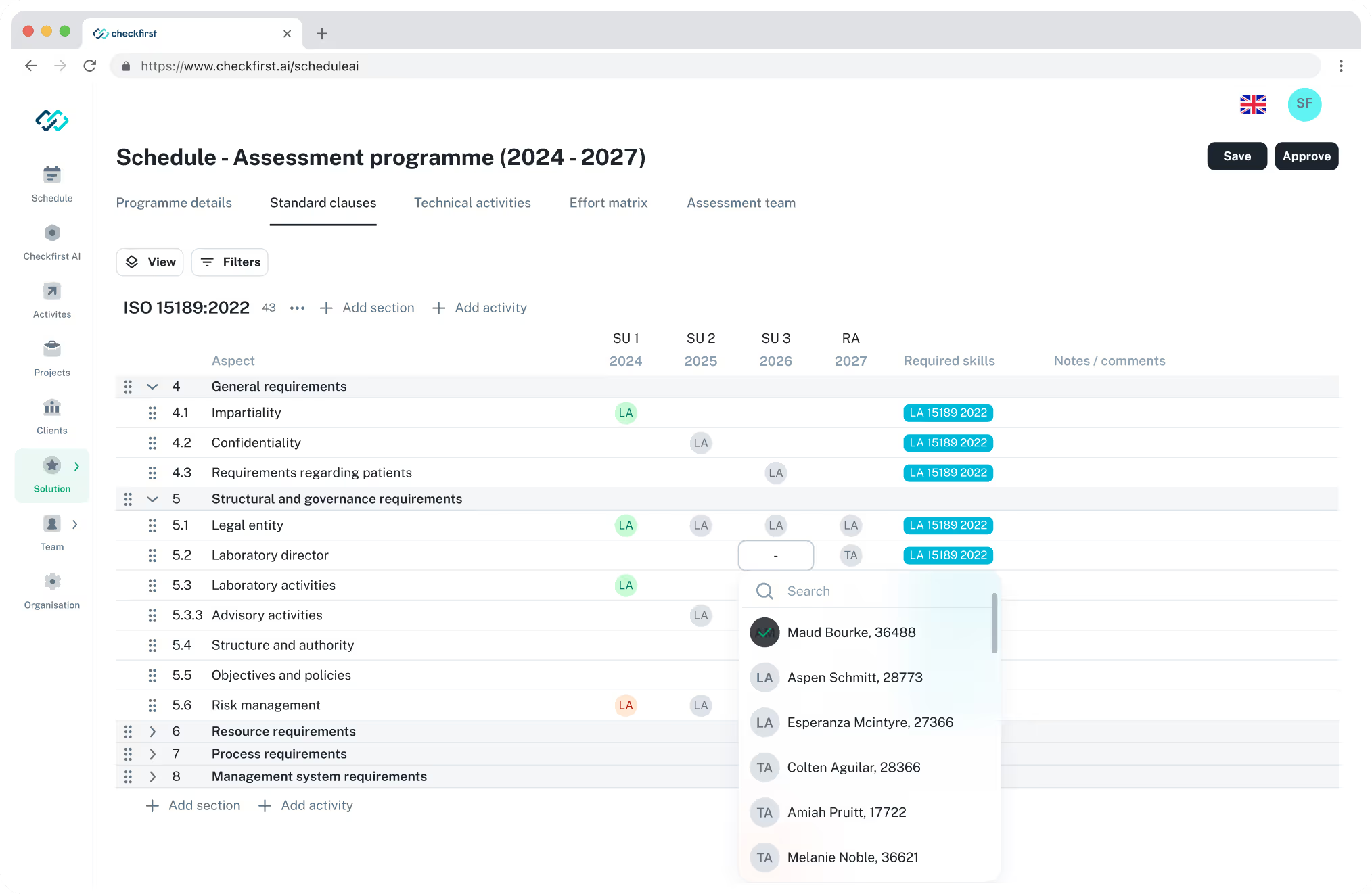
On the controls side, security and ICT vendors are often assessed against frameworks such as CSA CCM v4.0, SOC 2, ISO 27001 and more, with DORA specific requirements layered on top. Platforms like CheckFirst describe capabilities such as evaluating a vendor against 243 CSA controls in minutes, using tools like JinoXtreme CSA, ProvEye for external scans available through our AI-powered assessment suite, and Jino 360 for AI powered open web research to give a more complete supplier profile.
A Dora-aligned, five-step TPRM supplier assessment workflow. Helps risk teams streamline supplier reviews and decisions.
Translating DORA into supplier assessment checkpoints
When we align our templates to DORA, we do not just copy regulatory text, we translate it into supplier level checkpoints. That includes items like mapping ICT services to critical functions, checking for explicit subcontractor governance, requiring tested business continuity and disaster recovery plans, and insisting on reporting timelines for incidents that meet DORA thresholds.
Because DORA requires regular threat led penetration testing and ongoing monitoring, we also need to specify how often we will review each supplier, which testing evidence we accept, and how we track remediation. Without this clarity, TPRM becomes a paper exercise that fails under the first real incident.
4. Designing A Five Step TPRM Supplier Assessment Workflow For DORA
In our work with TIC and financial customers, we see the most sustainable TPRM programs use a simple five step workflow that everyone can understand and auditors can easily follow. It usually looks like this: classify the supplier and service, perform risk based due diligence, negotiate and lock in DORA aligned contracts, operationalize testing and monitoring, then review and adjust risk decisions regularly.
Each step has a clear owner and a clear output, such as a completed questionnaire, a risk rating, a set of mandatory clauses, or a monitoring dashboard. The key is to connect the data across steps, so our suppliers do not have to answer the same question five times and our own teams do not waste precious hours digging for old documents in shared drives.
Example: risk based branching in supplier assessments
Not every supplier needs the same depth of assessment, and DORA accepts proportionality as long as we can justify our choices. A five step workflow therefore needs branching logic that sends low risk, non critical vendors through a lighter review, while critical ICT providers go through detailed questionnaires, external scanning, and testing evidence review.
AI engines and structured questionnaires can guide this branching in real time, so risk managers do not have to make every call manually. This is where AI-powered TPRM tools show their value, flagging gaps like missing SOC reports or incomplete incident handling descriptions before an assessment is marked as complete.
5. Using AI To Cut Supplier Assessment Cycle Times From Months To Days
The biggest operational complaint we hear from risk teams is simple, vendor assessments drag on for weeks because document review and follow up questions consume calendar time. When an average vendor receives over thirty assessment requests per month and 84 percent of responses require follow up, everyone is stuck in email loops instead of managing risk.
AI is not a silver bullet, but it does handle repetitive work extremely well. Tools like VerifyAI type document review engines can scan COAs, policies, and certificates, then extract key data points and flag missing elements before audit day, while InspectAI style modules can capture inspection data in the field and push structured results back into TPRM records.
Where AI fits in the DORA supplier risk lifecycle
In a DORA context, we see AI fitting in four high impact moments, supplier classification, control mapping, document review, and monitoring. For example, an AI engine can read a vendor’s website and documents, infer which ICT services they provide, match them to DORA relevant controls and frameworks, and suggest an initial risk profile before a human reviewer steps in.
Once in production, AI can help identify anomalies in incident reports, capacity metrics, or inspection outcomes, alerting TPRM teams before a service failure becomes a DORA reportable event. This is not about replacing judgement, it is about giving risk owners better data in far less time.
6. Aligning Frameworks: CSA, SOC 2, ISO 27001 And DORA In One Supplier Assessment
For ICT suppliers, DORA is rarely the only requirement, most already hold or pursue certifications like SOC 2 or ISO 27001, and may complete CSA questionnaires for cloud services. A modern TPRM approach does not force suppliers to start from scratch every time, it reuses these standards and maps them to DORA expectations.
CheckFirst’s TPRM positioning shows one practical way to do this, assessing vendors against 243 CSA controls across 18 security domains, supported by external scans and web research modules. In our own programs, we take a similar approach, building a single control dictionary that links individual questions to multiple frameworks, which avoids fragmented supplier experiences and keeps evidence consistent.
Practical mapping tips for DORA aware supplier assessments
To keep assessments manageable, we recommend three practical steps, first, tag every questionnaire item with one or more framework references, including DORA articles where relevant. Second, identify which existing artefacts you will accept, for example, mapping SOC 2 trust principles and ISO 27001 Annex controls to DORA ICT control objectives.
Third, configure your TPRM platform so suppliers can upload one document once and link it to multiple control requirements. This keeps your evidence base strong without turning TPRM into a paperwork factory for every supplier relationship.
7. Scheduling Supplier Audits And Inspections Without 6am Fire Drills
DORA does not just care about paperwork, it cares about whether your critical suppliers can actually deliver under stress, which often means audits, on site inspections, and testing activities. In the TIC industry, this is where we see the most operational pain, with planners manually matching auditors to sites, juggling cancellations, and dealing with double bookings that hit at 6am.
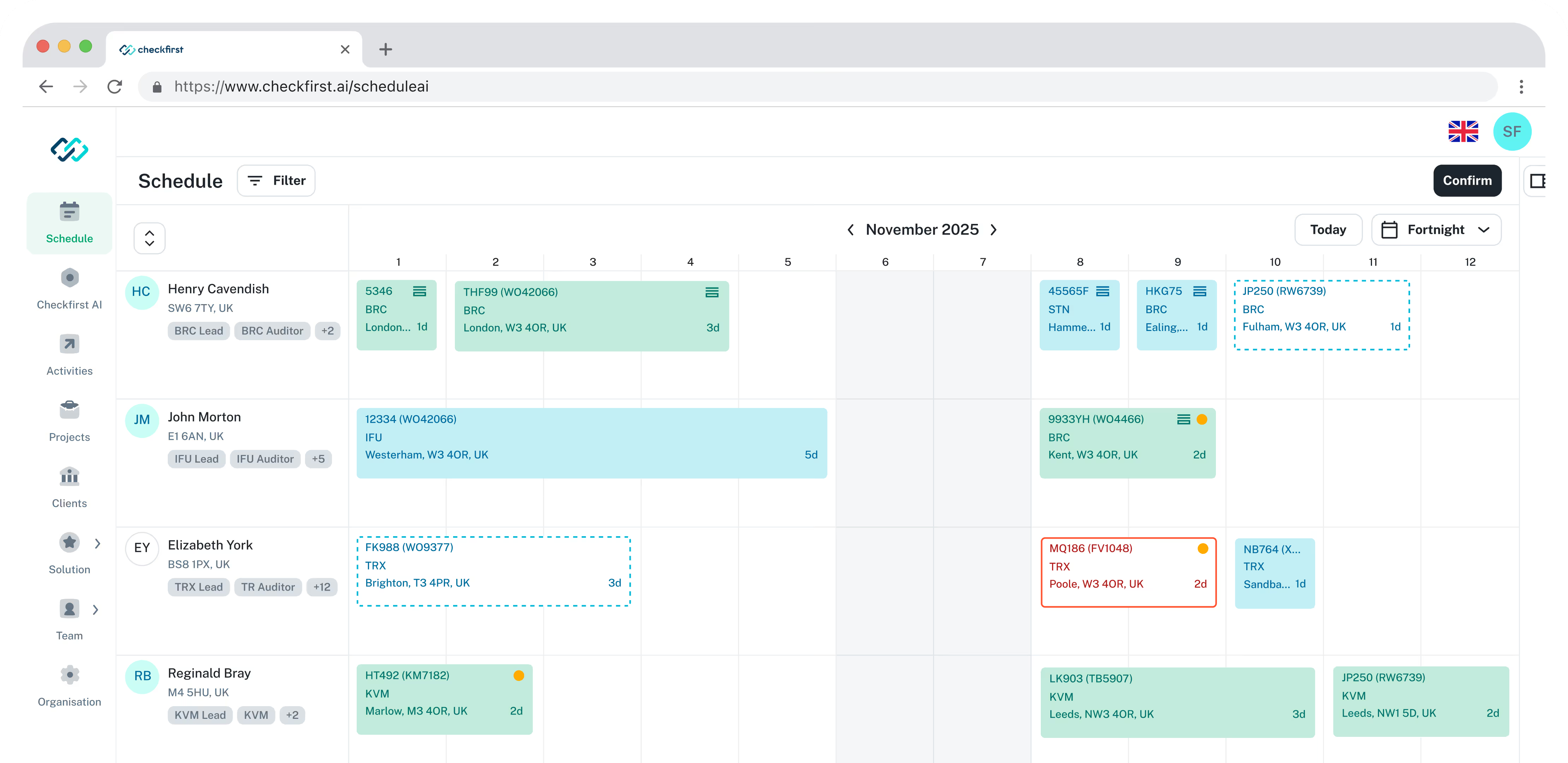
AI driven scheduling tools like ScheduleAI are designed for this exact pattern, auto assigning audits by skill, availability, cost, and region, then giving planners real time dashboards for utilization and lead times. While ScheduleAI pricing is not listed publicly, its promise is clear, what used to take a month of manual work is compressed into minutes, and rescheduling becomes a one click decision instead of a spreadsheet nightmare.
Why scheduling matters for DORA TPRM
From a DORA lens, unreliable audit scheduling turns into unreliable assurance, because tests slip, evidence is late, and remediation deadlines move without control. A supplier assessment program that looks complete on paper but fails to execute testing on time will not satisfy regulators during a post incident review.
By connecting supplier risk data with tools like ScheduleAI, we can prioritize audits for high risk vendors, ensure the right skills are on each job, and give managers live views into completion rates. This is exactly the kind of operational resilience story DORA expects us to tell, backed by real data, not just policy statements.
8. Continuous Monitoring: From One Off Assessments To Live Supplier Risk Management
A one off supplier questionnaire might satisfy procurement, but it does not satisfy DORA, especially when ICT services are critical to daily operations. What DORA expects is continuous monitoring for high risk vendors, which for us means a blend of periodic evidence refresh, real time alerts, and performance trend tracking across inspections and incidents.
In practice, this can include external scanning of exposed infrastructure, automated news and web monitoring for adverse events, and digestible dashboards that combine TPRM, audit, and incident data. Tools like ProvEye and Jino 360, mentioned in CheckFirst materials, point toward this direction, combining outside in and inside out views so risk owners do not miss early warning signs.
Building a DORA ready monitoring dashboard
For DORA, the monitoring challenge is not just technical, it is also about explainability, regulators will ask how we know our critical suppliers remain within risk appetite. A TPRM monitoring view therefore needs to show service coverage, current risk rating, last assessment and test dates, open remediation items, and any active incidents, ideally broken down by DORA relevant service categories.
We recommend starting with a small set of metrics so teams actually use the dashboards, then layering in more detail as data quality improves. The right outcome is simple, when an incident hits, we can answer in minutes which suppliers are involved, which controls they were supposed to meet, and what we are doing next.
9. Governance, Ownership, And Documentation That Survives Regulatory Scrutiny
Even the best designed supplier assessment workflow will fail under DORA if ownership is fuzzy and documentation is scattered. In 2026, most mature TPRM programs formalize a governance model that defines who owns the supplier risk policy, who signs off on critical vendor onboarding, and who maintains the evidence that assessments and monitoring actually happened.
We see three roles as essential, risk management for policy and appetite, procurement for sourcing and commercial levers, and business owners for service dependency decisions. A TPRM platform then acts as the system of record where assessments, contracts, test reports, and incident logs live, ready for internal and external audit without last minute scrambling.
Documentation risk under DORA
A common failure mode during inspections is not a missing control but missing proof that you assessed it for a specific supplier at a specific time. To avoid this, our supplier assessment process must log decisions clearly, store artefacts centrally, and make it easy to show progression over time when a vendor moves from high risk to acceptable risk after remediation.
Here, automation matters as much as policy, because humans will always forget to upload one attachment or log one call. AI supported tools can capture metadata automatically, tag documents by supplier and control, and surface incomplete records before an assessment is closed, which reduces painful surprises in front of regulators.
10. Measuring The Impact: Cost, Risk Reduction, And Vendor Experience
DORA compliance for TPRM is not cheap, with typical teams adding several full time employees at six figure cost levels to keep pace with supplier assessments and monitoring. The global average cost of a data breach is now around 4.88 million USD, which means poorly managed third party risk is expensive either way, whether you invest upfront or pay after an incident.
We advise treating TPRM supplier assessment as a measurable program, not an open ended cost. Useful metrics include time to approve a new critical supplier, number of overdue assessments, audit completion rates, supplier satisfaction with the process, and incident rates mapped to vendor controls, which together show whether the investment in tools and process is actually buying down risk.
Balancing risk management and supplier experience
One final point matters in 2026, vendor experience is strategically important, because your best ICT and inspection partners are in high demand and receive dozens of assessments every month. If your TPRM supplier assessment process is opaque, duplicative, and slow, you will either lose those suppliers or see them cut corners on responses just to keep up.
DORA does not require us to make life harder for suppliers, it requires us to be structured, evidence based, and transparent about risk expectations. By using AI and well designed workflows to remove chaos and manual noise, we can actually make assessments clearer for vendors while giving our own teams the control, accountability, and audit trail they need.
Conclusion
TPRM supplier assessment under DORA in 2026 is no longer an optional layer of bureaucracy, it is a core part of operational resilience and regulatory credibility. With hundreds of suppliers, tighter supervisory expectations, and real financial exposure, manual TPRM processes simply cannot keep pace.
By combining a clear DORA aligned framework with AI powered assessment, inspection, and scheduling tools, we can reduce assessment cycle times, improve supplier experience, and, most importantly, gain genuine visibility into third party risk. The chaos does not disappear on its own, it disappears when we design TPRM to work at the scale and speed our organizations now require.
Looking to make your TPRM program DORA-ready? Start with CheckFirst’s AI-driven security assessments to evaluate suppliers against CSA controls in minutes. Need a fully managed approach? Explore our managed TPRM service or view our pricing plans to get started. Learn more about our team and our mission to automate critical compliance workflows.

.avif)